
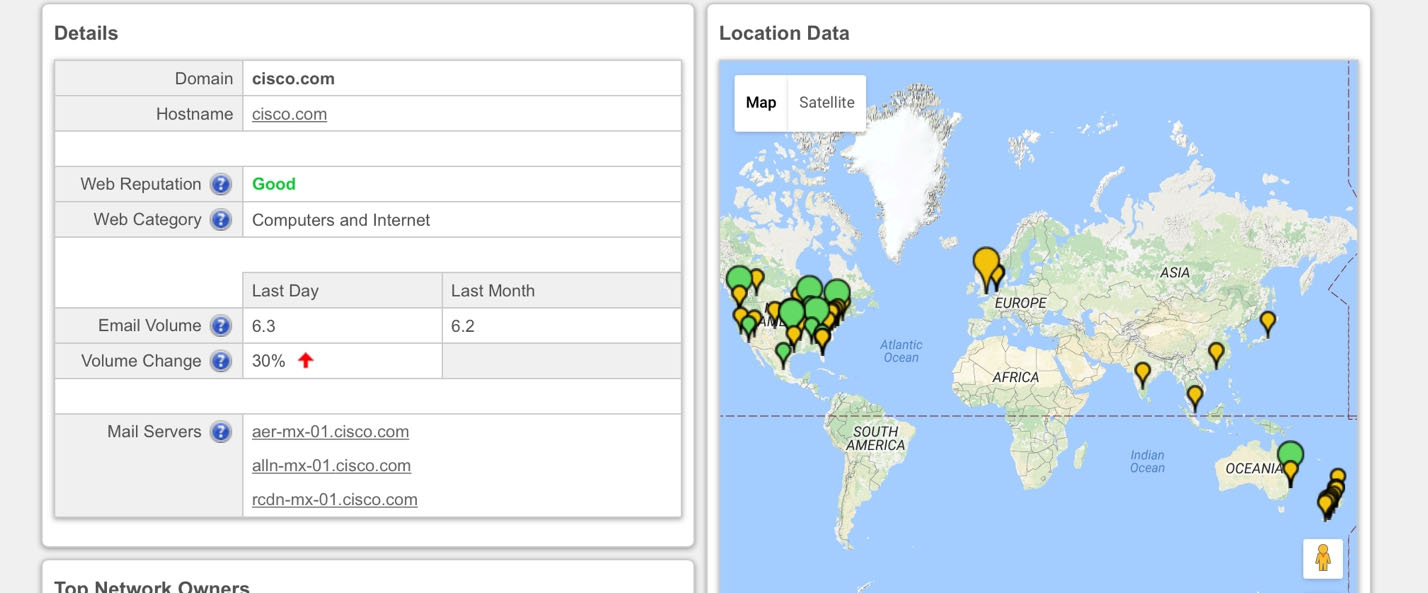
Refer to the exhibit. We have performed a malware detection on the Cisco website. Which statement about the result is true?
- A. The website has been marked benign on all 68 checks.
- B. The threat detection needs to run again.
- C. The website has 68 open threats.
- D. The website has been marked benign on 0 checks.
Answer : A
Explanation:
Example:
https://www.virustotal.com/en/url/df05d8e27bd760c33dc709951a5840cc6578d78d544d869890b7b94ea21e46b0/analysis/1368183553/
During which phase of the forensic process is data that is related to a specific event labeled and recorded to preserve its integrity?
- A. collection
- B. examination
- C. reporting
- D. investigation
Answer : A
Explanation:
The basic phases of the forensic process are: collection, examination, analysis, and reporting. During collection, data related to a specific event is identified, labeled, recorded, and collected, and its integrity is preserved. In the second phase, examination, forensic tools and techniques appropriate to the types of data that were collected are executed to identify and extract the relevant information from the collected data while protecting its integrity. Examination may use a combination of automated tools and manual processes. The next phase, analysis, involves analyzing the results of the examination to derive useful information that addresses the questions that were the impetus for performing the collection and examination. The final phase involves reporting the results of the analysis, which may include describing the actions performed, determining what other actions need to be performed, and recommending improvements to policies, guidelines, procedures, tools, and other aspects of the forensic process.
Reference:
http://itlaw.wikia.com/wiki/Forensic_process
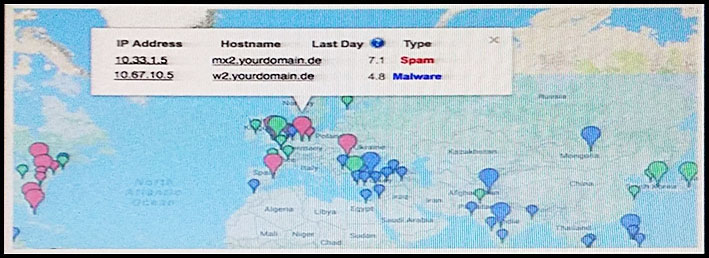
Refer to the exhibit. A customer reports that they cannot access your organization"™s website. Which option is a possible reason that the customer cannot access the website?
- A. The server at 10.33.1.5 is using up too much bandwidth causing a denial-of-service.
- B. The server at 10.67.10.5 has a virus.
- C. A vulnerability scanner has shown that 10.67.10.5 has been compromised.
- D. Web traffic sent from 10.67.10.5 has been identified as malicious by Internet sensors.
Answer : D
Explanation:
Every firewall has its own database where it maintains the website reputation on terms of security, ease of access, performance etc and below certain score
(generally 7 in case of Cisco), firewalls block access to the sites. For example, you can visit www.senderbase.org and enter name of any website and you will see the reputation of that website.
You see 100 HTTP GET and POST requests for various pages on one of your webservers. The user agent in the requests contain php code that, if executed, creates and writes to a new php file on the webserver. Which category does this event fall under as defined in the Diamond Model of Intrusion?
- A. delivery
- B. reconnaissance
- C. action on objectives
- D. installation
- E. exploitation
Answer : D

